Blog
How to prevent ATM cash-out attacks in your payments environments
Whether you are a financial institution or payment processor, having end-to-end visibility into your payments systems is mandatory when it comes to preventing ATM cash-out attacks.

September 7, 2018
By Stacy Gorkoff, Vice President of Marketing, Inetco Systems Ltd.
On August 10, when the FBI warned that a global ATM cash-out scheme was about to occur, many banks, IADs and payment processors went on high alert. While this did not stop criminals in 28 countries from making off with more than $13.5 million from an Indian bank, it did bring up the importance of early warning fraud systems and layered defense mechanisms.
A day before the ATM cash-out attack occurred, the FBI released a confidential alert to banks that warned of large scale, "unlimited operation" schemes to come.
|
| Figure 1: An example of how malware authorizes transactions without talking to the back-end |
The alert further stated that these types of schemes occur when cybercriminals attack a financial institution or payment processor by installing malware on the host switch and exploiting network access in order to acquire customer debit or card account information.
While the alert focused on the parameters surrounding the potential threat, it also identified increasing attacks of this nature happening in the U.S.
Faced with increasingly sophisticated fraud techniques and information security risks, financial institutions, IADs and payment processors must adopt strategies that give them the ability to detect debit card and ATM fraud as it is unfolding — not after the damage is done. To prevent ATM cash-out attacks on financial institutions or payment processors, industry best practices suggest:
- Implementing an incident management system, and preparing an incident response plan for rapid deployment in case of cyberintrusion.
- Identifying third-party risks, such as the party that drives the bank’s ATMs and what security controls are in place for unusual volume activity or unusual activity during non-peak time.
- Establishing a known, clean baseline for all ATM hardware that can be used as a measurement to determine any deviations.
These best practices are only the tip of the iceberg when it comes to preventing ATM cash-out attacks, but they do highlight the importance of making real-time, transaction-level monitoring and alerting a part of your payments security strategy.
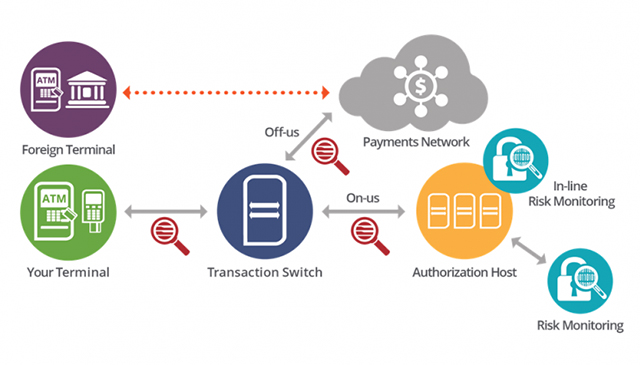 |
| Figure 2: A reliable, early warning fraud solution monitors the entire transaction path to detect anomalies in real-time. |
With end-to-end visibility into both the front end and back end of every transaction, FIs can detect anomalous behaviors such as rogue switches approving fraudulent transactions — without those messages ever making it to the authorization host.
In the case of switch malware that removes fraud controls set around maximum withdrawal amounts or high-velocity transaction use, transaction-level monitoring can pick up these patterns and real-time alerts can be set based on the various message types and fields contained within each transaction. Example alerts include:
- X number of international transactions within Y hours.
- X number of transaction by international cards in the last Y hours.
- X or more bank cards carrying out withdrawals on the same foreign terminal within Y minutes.
- X number of consecutive magnetic stripe transactions (instead of chip) from a specific ATM.
- "Fake processing," where cash withdrawals are observed on an ISO link with no matching back-end database transaction.
Whether you are a financial institution or payment processor, having end-to-end visibility into your payments systems is mandatory when it comes to preventing ATM cash-out attacks. Current industry best practices suggest implementing a real-time, transaction-level monitoring and alerting solution to help combat these increasingly sophisticated fraud techniques and information security risks.
 ChatGPT
ChatGPT Grok
Grok Perplexity
Perplexity Claude
Claude













